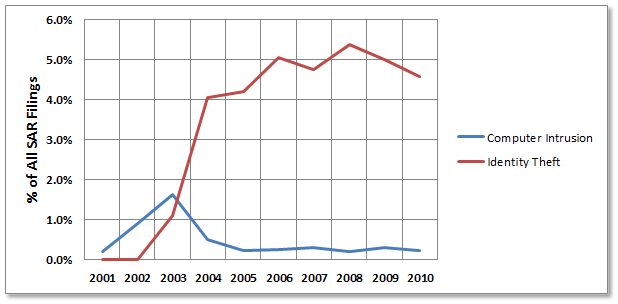
SAR Filings – Computer Intrusion vs. Identity Theft
The Financial Crimes Enforcement Network (FinCEN) publishes a statistical summary and review of all suspicious activity report (SAR) filings a couple of times per year. The latest one was just released in May covering the 10 year period from 1/1/2001 through 12/31/2010. I thought it might be interesting to see how the category of Computer Intrusion (Part III, item 35 f) compared with Identity Theft (Part III, item 35 u) during that period of time:
As expected, reported incidents of identity theft increased sharply and remain relatively high today…no surprises there. What did surprise me though is the low reported incidents of computer intrusion over the past 5 years. (The initial blip in 2003 was due to the fact that when the Computer Intrusion category was added in 2000, it initially defined an intrusion as “gaining access or attempting to gain access to a computer system of a financial institution”. That meant that each time the firewall blocked an attempt, it had to be reported. Obviously this proved to be extremely labor intensive, and the verbiage was changed in 2003 to define intrusion as actually gaining access to the system.)
I suppose the lesson here* is that financial institutions are doing a far better job securing their networks then they are securing their customer data, which leads me to the conclusion that the vast majority of identity theft must be occurring outside the protected perimeter of the institutions’ networks. Remember, you must protect your data at every stage of its existence; during processing, in transit, and in storage, and regardless of its physical or electronic nature.
By the way, the newest SAR form for depository institutions is here. It was just updated in March, and institutions must use this to replace the older form (dated July 2003) by September 30th of this year. I compared the two forms side by side to see what the differences were, but couldn’t find a single change besides the date, so I’m not sure why the new form is required, but it is.
*Of course another possibility is that computer intrusions are simply being under-reported, but since most financial institutions have been subjected to regular audits, penetration tests and examinations, I believe that the low incidence is probably accurate.