Cybersecurity – Beyond the Assessment
The FFIEC Cybersecurity Assessment Tool has been out since 2015, and by now almost all financial institutions have completed it at least once, some as many as 3-4 times. Although most of the examiner feedback we’ve gotten indicates that simply completing is all regulators are looking for at this time, the FFIEC made it clear that competing the assessment is only the first step. It is designed to be a means to an end, not the end itself. The goal of the assessment process is a plan consisting of specific actions the institution can, and ultimately must, take to strengthen their cybersecurity posture. Fortunately, the tool provides those specific actions, called declarative statements. Unfortunately, there are a total of 497 declarative statements spread among 5 domains:
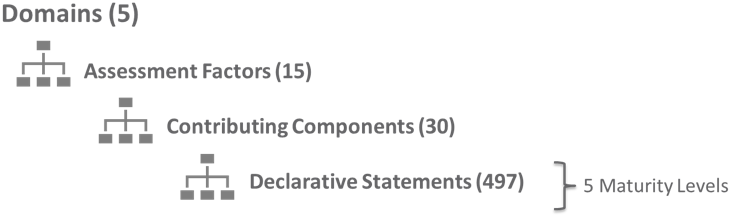
So selecting the right domain (or domains) is the first challenge, followed by somehow drilling down to the exact statements that have the greatest impact.
The 5 Cybersecurity Steps
To best approach this challenge, let’s take a step back and re-visit the guidance. The FFIEC specifies 5 steps in the cybersecurity process:
- Assess maturity and inherent risk
- Identify gaps in alignment
- Determine desired state of maturity
- Implement plans to attain and sustain maturity
- Reevaluate
If all you are doing is skipping from step 1 to step 5 (i.e. just reassessing each year), you are missing the point of the exercise. Step 4 (the action plan) is actually the goal, but to get there you must add a missing step to the process, we’ll call it step 1a:
- Assess maturity and inherent risk
a. Interpret and analyze results - Identify gaps in alignment
- Determine desired state of maturity
- Implement plans to attain and sustain maturity
- Reevaluate
According to the FFIEC, interpreting and analyzing assessment results means that management should review the institution’s inherent risks and the control maturity “…for each domain to understand whether they are aligned.” Here is where the initial challenge begins for most institutions, because the assessment tool does not provide any direct correlation between individual risks and specific controls, or even risks and domains. This critical process is left to the assessor (you). Certainly some controls and control groups are more effective against certain risks, but there really isn’t a one-to-one relationship between risks and controls. In fact, in a layered security approach to risk management it’s really a one-to-many relationship; one risk requires multiple controls. What we suggest is that you try to identify the common denominators between high risk areas, and then focus on the domain or domains that contain those common denominators.
For example, let’s say your risks are mostly least or minimal, with a few moderate. (This is what we generally see with community FI’s.) Further, let’s say that after you interpret and analyze the results, one of the common denominators with the higher (moderate) risk items is that they all rely on third-party relationships (again, very common with community FI’s). In this example, identifying declarative statements in Domain 4 – External Dependency Management would be most appropriate. But how do you get from the domain level all the way down to the declarative statement level? Here is the next challenge, because in order to identify specific controls you have to drill down into the domain to get to specific declarative statements.
Continuing with our example, since we’ve decided that additional controls in domain 4 would be most effective, let’s take a deeper dive. Here is how Domain 4 breaks down:
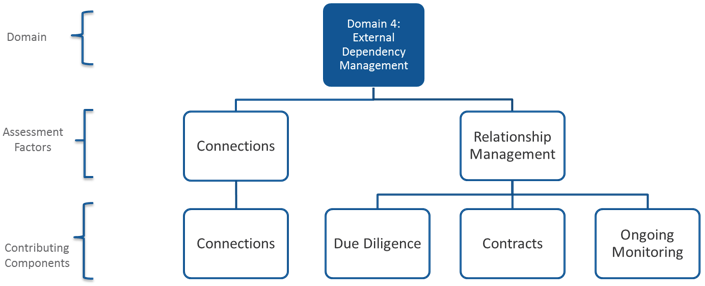
Let’s further assume that of the 2 Assessment Factors, the Relationship Management section is more relevant to us than Connections, since we have a pretty good idea of who we connect to and how we connect (a data flow diagram is the key to documenting information flow to external parties). Under that section, there are a total of 35 declarative statements distributed among three Contributing Components, which can be loosely described as pre-contract (Due Diligence), legal (Contract), and Ongoing. While all three are important, let’s say that since we already have a contractual relationship with the vendor(s), we’ve decided that ongoing monitoring should be our focus for increasing control maturity. Now we are down to only 11 declarative statements, and all we do from here is simply work our way up from Baseline (containing 3 statements) which is the minimum required level, through Evolving (4 statements), and into Intermediate (2 statements). According to the FFIEC, intermediate level controls are more than adequate to off-set moderate and even significant risk levels, so it’s unlikely you’ll have to progress beyond that.
In Summary
To summarize, in order to “implement a plan to attain and sustain maturity”, you must:
- Analyze the results of your assessment
- Find the common denominators among your increased risk areas
- Identify the domain or domains most effective against those common denominators
- Select the most relevant Assessment Factor(s) within those domains
- Select the most appropriate Contributing Component(s) within the Assessment Factors
- Identify specific Declarative Statements from among the 5 Maturity Levels, starting at Baseline and working up
The statements identified become your “plan to attain and sustain,” once they are assigned to a responsible party or group, and followed to completion. Next time you reassess, you’ll be able to check a few more statements, demonstrating your commitment to increasing your cybersecurity maturity level. And a steady increase is what you’ll need to keep pace with the increasing cyber threat environment.


